Penetration testing stories - Page 3

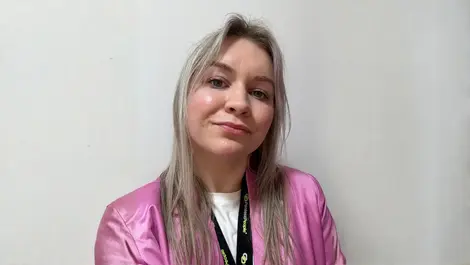
Reversec names Åse Holmberg Zetterlund as Chief Executive
Last month
#
devops
#
partner programmes
#
supply chain
Cyber consultancy Reversec has named former Accenture executive Åse Holmberg Zetterlund as CEO to drive its next phase of global expansion.

Why cybersecurity needs women from non-tech careers
Last month
#
ransomware
#
devops
#
advanced persistent threat protection
Cybersecurity is missing vital human insight; drawing in women and non‑STEM talent could close both the threat and perspective gaps.
The power of representation in cybersecurity
Last month
#
firewalls
#
devops
#
network security
As cyber threats grow, more women are entering security roles, yet leadership remains male-dominated, risking lost talent and weaker defences.

LevelBlue unveils flexible funds-based cyber IR retainer
Last month
#
ransomware
#
devops
#
socs
LevelBlue launches Resilience Retainer, a flexible funds-based cyber incident response service with rapid SLAs and rollover security spend.

Why diversity in cybersecurity leadership is vital
Last month
#
devops
#
apm
#
risk & compliance
Homogeneous cybersecurity leadership is a critical, overlooked point of failure; true defence in depth demands diversity as a core control.
F5 Labs unveils monthly AI model security leaderboards
Last month
#
data protection
#
devops
#
application security
F5 Labs launches monthly AI security leaderboards, ranking popular models on new indices of risk, resilience and cost under live attack.

Security debt surges as legacy vulnerabilities pile up
Thu, 26th Feb 2026
#
data protection
#
devops
#
application security
Security debt hits 82% of organisations as legacy flaws linger over a year, with third-party code driving most critical vulnerabilities.
Horizon3.ai names Dan Bird MBE Field CTO for EMEA cyber push
Wed, 25th Feb 2026
#
devops
#
digital transformation
#
hyperscale
Horizon3.ai appoints defence veteran Dan Bird MBE as EMEA field CTO to sharpen offensive security amid rising regional cyber threats.

Simbian unveils AI agent for continuous pentesting
Fri, 20th Feb 2026
#
data protection
#
devops
#
application security
Simbian launches an AI Pentest Agent that runs continuous, adaptive penetration tests, promising faster, context-aware vulnerability detection.

CISOs warn AI adoption outpaces ability to secure it
Fri, 20th Feb 2026
#
data protection
#
devops
#
digital transformation
CISOs say AI is spreading faster than they can secure it, with poor visibility and skills gaps leaving critical systems increasingly exposed.

3DiVi sets four-layer defence for face authentication
Thu, 19th Feb 2026
#
data protection
#
devops
#
surveillance
3DiVi unveils four-layer defence model to harden face authentication against deepfakes and spoofing as remote ID checks surge globally.

CompTIA launches SecAI+ to tackle AI security skills
Wed, 18th Feb 2026
#
malware
#
data protection
#
devops
CompTIA unveils SecAI+ certification to equip cybersecurity professionals with AI security, risk management and governance skills.
Hackers ditch noisy ransomware for stealthy data theft
Thu, 12th Feb 2026
#
firewalls
#
data protection
#
dr
Hackers are abandoning noisy ransomware to quietly steal data, as a report finds 80% of top attack techniques now focus on evasion.

Cyber firms face 'verification crisis' on real risk
Wed, 11th Feb 2026
#
firewalls
#
devops
#
digital transformation
Cyber firms warned over 'verification crisis' as tools flag floods of flaws but only 0.47% prove exploitable, leaving real risk unresolved.

Bitget, BlockSec unveil new security standard for UEX
Wed, 11th Feb 2026
#
devops
#
surveillance
#
crypto
Bitget and BlockSec launch a UEX Security Standard, urging provable, system-wide safeguards for unified multi-asset trading platforms.

SpecterOps unveils BloodHound Scentry identity risk service
Wed, 11th Feb 2026
#
devops
#
pam
#
cloud security
SpecterOps has launched BloodHound Scentry, a managed identity risk service to find and remediate attack paths across complex environments.

Flare sees rapid MSSP uptake of external threat intel
Fri, 6th Feb 2026
#
devops
#
socs
#
partner programmes
Flare reports 114% annual growth among MSSPs as providers consolidate threat intelligence tools to boost services without extra analyst strain.

Routine internal access, not exploits, drives cyber risk
Wed, 4th Feb 2026
#
malware
#
firewalls
#
devops
Routine admin tools, not exotic exploits, let attackers race across networks, compromising over half of systems in under an hour.

AI-driven attacks overwhelm security teams in 2026
Fri, 30th Jan 2026
#
devops
#
advanced persistent threat protection
#
socs
AI-fuelled cyberattacks overwhelm defenders as false positives swamp security teams and critical threats slip through in 2026, Hadrian warns.

AI security drives demand for faster pentesting models
Fri, 30th Jan 2026
#
devops
#
digital transformation
#
cloud security
AI security fears and rapid release cycles are pushing firms to demand faster, deeper pentesting - and many are ready to ditch existing vendors.